Security researchers say they used a $150 mask to break the Face ID facial recognition system that locks Apple's new iPhone X. The work may be a significant, it may be little more than a stunt with few real-world consequences, or it could possibly be something in the middle. So far, it's impossible to know because the researchers have evaded key questions about how they went about breaking into the device.
The supposed hack was carried out by researchers from Vietnamese security firm Bkav, which in 2009 demonstrated a way to bypass face-based authentication in Toshiba and Lenovo laptops. On Friday, company researchers published a video showing them unlocking an iPhone X by presenting it with a custom-made mask instead of the live human face that Apple has repeatedly insisted is the only thing that can satisfy the requirements of the facial recognition system.
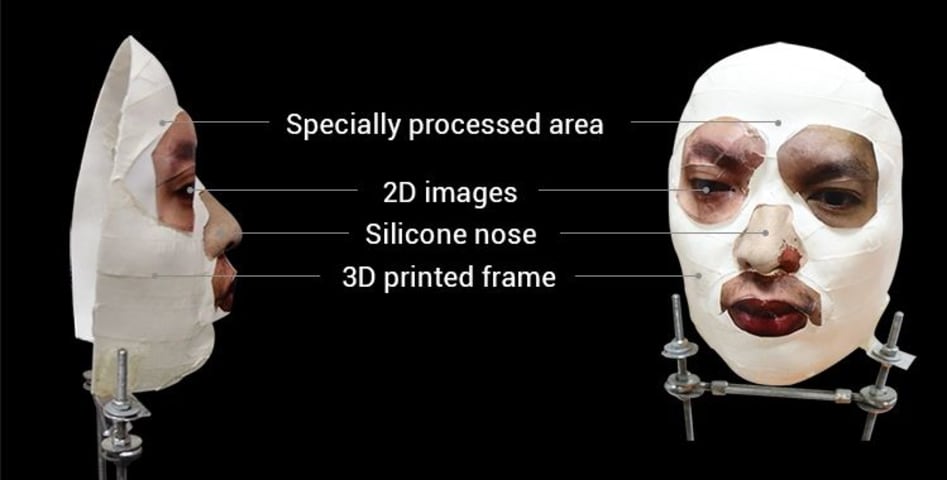
The researchers said they designed their mask using 2D and 3D printers and that an artist made the nose by hand using silicone materials. Other features of the mask used 2D images and "special processing on the cheeks and around the face, where there are large skin areas" in a successful attempt to defeat the artificial intelligence Face ID uses to distinguish real faces from images, videos, or masks.
"It is quite hard to make the 'correct' mask without certain knowledge of security," a Bkav representative wrote in an e-mail to Ars. "We were able to trick Apple's AI, as mentioned in the writing, because we understood how their AI worked and how to bypass it."
The truth is out there
The video and accompanying press release omitted key details that are needed for other researchers to assess if the results represent a true bypass of an authentication system Apple has spent years developing. One of the most important details is whether the mask successfully unlocked the iPhone immediately after it was set up to use the real human face for authentication or if the bypass succeeded only over a period of time following the face enrollment. The distinction is crucial. According to a white paper Apple published earlier this month, Face ID takes additional captures over time and uses them to augment enrolled Face ID data. If the researchers trained Face ID over time to work with the mask, they were giving themselves an advantage a real-world attacker wouldn't have.
Another important consideration is how the mask was made. Did, for instance, the artist or any of the researchers have to have access to the real face the mask was based on? Did the human target sit for measurements or the taking of a mold? Or, on the other hand, was the mask solely crafted using images or videos that could be taken without the target's knowledge or consent? Again, the answers are crucial because if the mask could only be created with the help of the target, the bypass doesn't represent a meaningful hack.
Throughout the weekend, Ars pressed Bkav representatives repeatedly to describe these and other details. As the following exchange demonstrates, the representatives deflected and at times outright evaded the questions:
Ars: Were you able to use the mask to unlock the iPhone immediately after freshly enrolling the real face? The reason I ask is that, according to Apple's whitepaper, Face ID will take additional captures over time and augment its enrolled Face ID data with the newly calculated mathematical representation. Can you describe precisely how you went about conducting this experiment? Bkav: It does not matter whether Apple Face ID “learns” new images of the face, since it will not affect the truth that Apple Face ID is not an effective security measure. However, we knew about this “learning,” thus, to give a more persuasive result, we applied the strict rule of "absolutely no passcode" when crafting the mask. Ars: Can you explain why your hack worked but the ones attempted by Wired magazine failed? Bkav: Because... we are the leading cyber security firm ;) It is quite hard to make the "correct" mask without certain knowledge of security. We were able to trick Apple's AI, as mentioned in the writing, because we understood how their AI worked and how to bypass it. As in 2008, we were the first to show that face recognition was not an effective security measure for laptops. Ars: Are the dimensions of a person's face needed? How would those be obtained without a target sitting for them? Bkav: The 1st point is, everything went much more easily than you expect. You can try it out with your own iPhone X, the phone shall recognize you even when you cover a half of your face. It means the recognition mechanism is not as strict as you think, Apple seems to rely too much on Face ID’s AI. We just need a half face to create the mask. It was even simpler than we ourselves had thought. Apple has done this not so well. I remember reading an article on Mashable, in which Apple told that iPhone X had been planned to be rolled out in 2018, but the company then decided to release it one year ear